dnstwist
This Integration is part of the Dnstwist Pack.#
Supported versions
Available on Cortex XSOAR and Cortex XSIAM.
Cortex XSOAR interfaces with dnstwist to research what sort of trouble users can get in trying to type a domain name. Find similar-looking domains that adversaries can use for attacking. dnstwist detect typosquatting, phishing attacks, fraud, and corporate espionage. Useful as an additional source of targeted threat intelligence.
The integration uses Docker image demisto/dnstwist:1.0 .
Use Cases
dnstwist takes in a domain name as a seed, generates a list of potential phishing domains, and then checks to see if they are registered.
Additionally, it can test if the mail server from MX (mail exchange) record can be used to intercept misdirected corporate e-mails, and it can generate fuzzy hashes of the web pages to see if they are live phishing sites.
Configure dnstwist on Cortex XSOAR
- Navigate to Settings > Integrations > Servers & Services .
- Search for dnstwist.
-
Click
Add instance
to create and configure a new integration instance.
- Name : a textual name for the integration instance.
- Click Test to validate the new instance.
Commands
You can execute these commands from the Cortex XSOAR CLI, as part of an automation, or in a playbook.
After you successfully execute a command, a DBot message appears in the War Room with the command details.
1. Check domain variations
Checks domain variations.
Base Command
dnstwist-domain-variations
Input
| Argument Name | Description | Required |
|---|---|---|
| domain |
The domain name for which to check for variations.
|
Required |
| limit |
Maximum number results to return in the context. This helps manage browser performance. The Markdown entry will display all results.
|
Optional |
|
whois
|
Whether to perform a query for the Whois creation or last updated time (slow).
|
Optional |
Context Output
| Path | Description |
|---|---|
| dnstwist.Domain.Domains.Name |
Domain name variations.
|
| dnstwist.Domain.Domains.IP |
IP addresses that resolved to domain name variations.
|
| dnstwist.Domain.Domains.DNS-MX |
Mail exchange records that resolved to domain name variations.
|
|
dnstwist.Domain.Domains.DNS-NS
|
Server names that resolved to domain name variations . |
|
dnstwist.Domain.Domains.WhoisUpdated
|
Whois updated for domain name variations . |
|
dnstwist.Domain.Domains.WhoisCreated
|
Whois created for domain name variations.
|
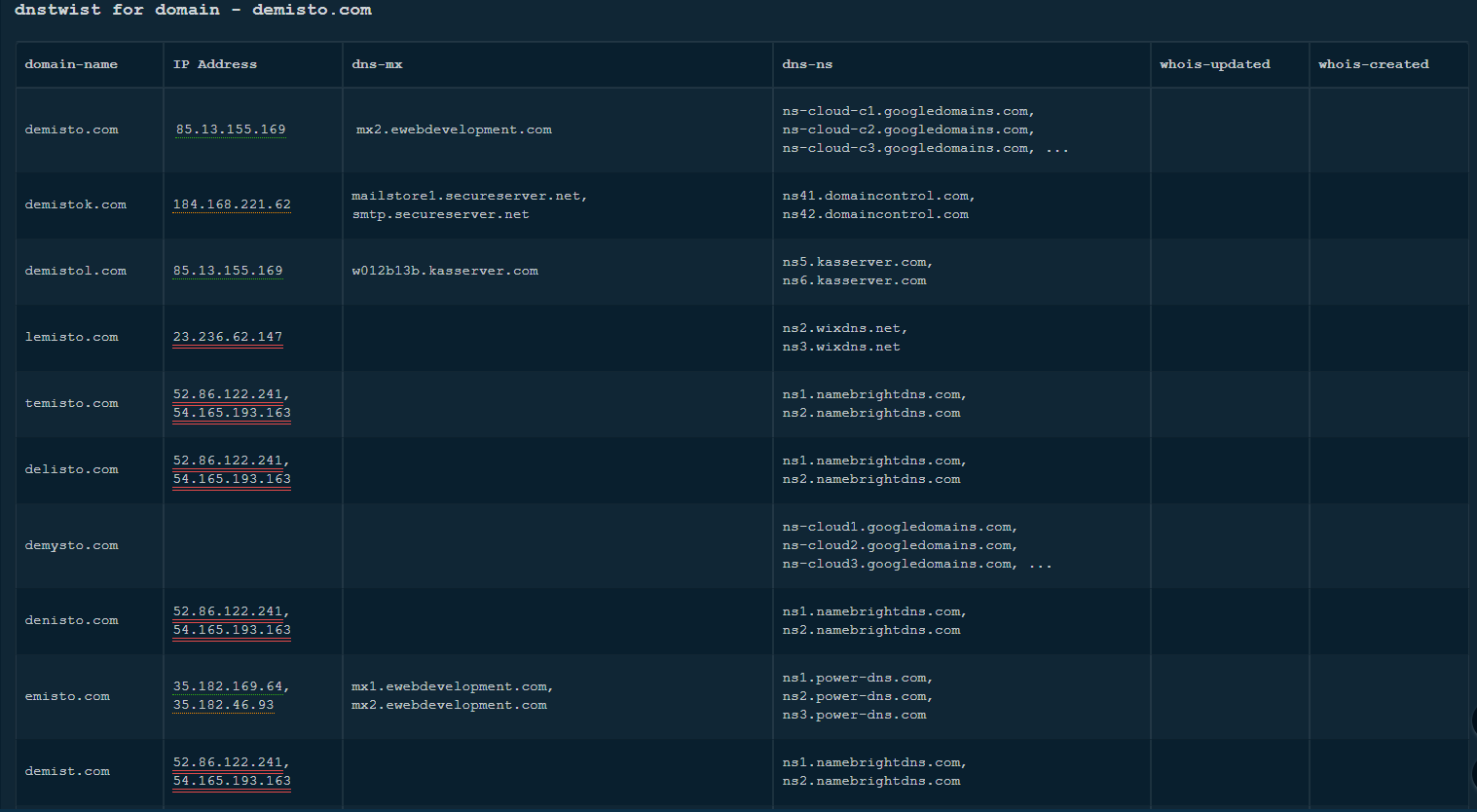
Command Example
!dnstwist-domain-variations domain=demisto.com
Context Example
"dnstwist":
{
"Domain": {
"Name": "demisto.com",
"IP" : ["85.13.155.169"]
"Domains": [
{
"Name": "demistok.com",
"IP": ["52.86.122.241","54.165.193.163"]
},
{
"Name": "demistol.com",
"IP": ["85.13.155.169"]
}
]
}
}