ReversingLabs TitaniumCloud (Deprecated)
This Integration is part of the ReversingLabs TitaniumCloud Pack.#
Deprecated
Use the ReversingLabs TitaniumCloud v2 integration instead.
Overview
Use the TitaniumCloud Integration Malware Analysis Platform to increase detection, analysis and response efficiency by identifying files with global goodware and malware database. It is a powerful threat intelligence solution with up-to-date, threat classification and rich context on over 6B goodware and malware files.
This integration was integrated and tested with ReversingLabs TitaniumCloud™.
Use Cases
- Provide a file reputation status for a file to prepare for emerging threats by monitoring malware.
Prerequisites
You need to obtain the following ReversingLabs TitaniumCloud information.
-
Base URL for malware presence
:
- Preconfigured on Cortex XSOAR - https://ticloud-aws1-api.reversinglabs.com
-
Base URL for extended RL Data
:
- Preconfigured on Cortex XSOAR - https://ticloud-cdn-api.reversinglabs.com
-
Credentials for ReversingLabs TitaniumCloud
- UserName
- Password
Configure ReversingLabs Titanium Cloud on Cortex XSOAR
- Navigate to Settings > Integrations > Servers & Services .
- Search for ReversingLabs Titanium Cloud.
-
Click
Add instance
to create and configure a new integration instance.
- Name : a meaningful name for the integration instance.
- Base URL for malware presence : https://ticloud-aws1-api.reversinglabs.com
- Base URL for extended RL Data : https://ticloud-cdn-api.reversinglabs.com
- Credentials and Password : paste the username and password for your TitaniumCloud account.
- Click Test to validate the URLs and connection.
Commands
You can execute these commands from the Cortex XSOAR CLI, as part of an automation, or in a playbook. After you successfully execute a command, a DBot message appears in the War Room with the command details.
- Retrieve malware presence status of a sample: file
Retrieve malware presence status of a sample: file
Get the ReversingLabs malware presence status for a file. This service supports single has queries and the option to return additional response data. The ReversingLabs Malware Statuses are:
- Malicious
- Suspicious
- Known
- Unknown
Command Example
!file file="c4ab31a0e6bee10933367e74b8af630daed5bd5e" extended="true"
Input
| Parameter | Description | Required? |
| file | The hash that you want to get reputation data for. Hexadecimal representation of SHA-1, SHA-256, SHA-512, or MD5 digest. | required |
| extended | Directs the data browser to return richer response schema, with additional classifications and facts about the queried sample. If you do not specify this parameter in the command, the default is false . | optional |
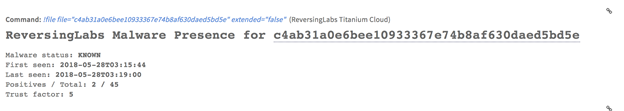
Human Readable Output (extended = false)
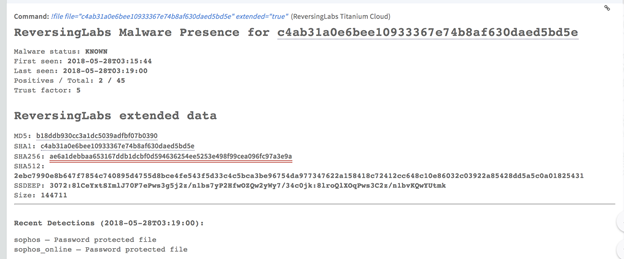
Human Readable Output (extended = true)
Context Output
|
Parameter |
Description |
|
File.MD5 |
Bad hash detected. |
|
File.SHA1 |
Bad hash SHA-1. |
|
File.Malicious.Vendor |
For malicious files, the vendor that made the decision. |
|
File.Malicious.Detections |
For malicious files, the total number of detections. |
|
File.Malicious.TotalEngines |
For malicious files, the total number of engines. |
|
DBotScore.Indicator |
The indicator that is being tested. |
|
DBotScore.Type |
Indicator type. |
|
DBotScore.Vendor |
Vendor used to calculate the score. |
|
DBotScore.Score |
The actual score. |
Raw Output
"malware_presence" : {
"first_seen" : "2018-05-28T03:15:44" ,
"last_seen" : "2018-05-28T03:19:00" ,
"query_hash" : {
sha1 : c4ab31a0e6bee10933367e74b8af630daed5bd5e
} ,
"scanner_count" : 45 ,
"scanner_match" : 2 ,
"scanner_percent" : 4.44444465637207 ,
"status" : "KNOWN" ,
"threat_level" : 0 ,
"trust_factor" : 5 ,
}
}