Cortex ASM - Vulnerability Management Enrichment
This Playbook is part of the Cortex Attack Surface Management Pack.#
Deprecated
No available replacement.
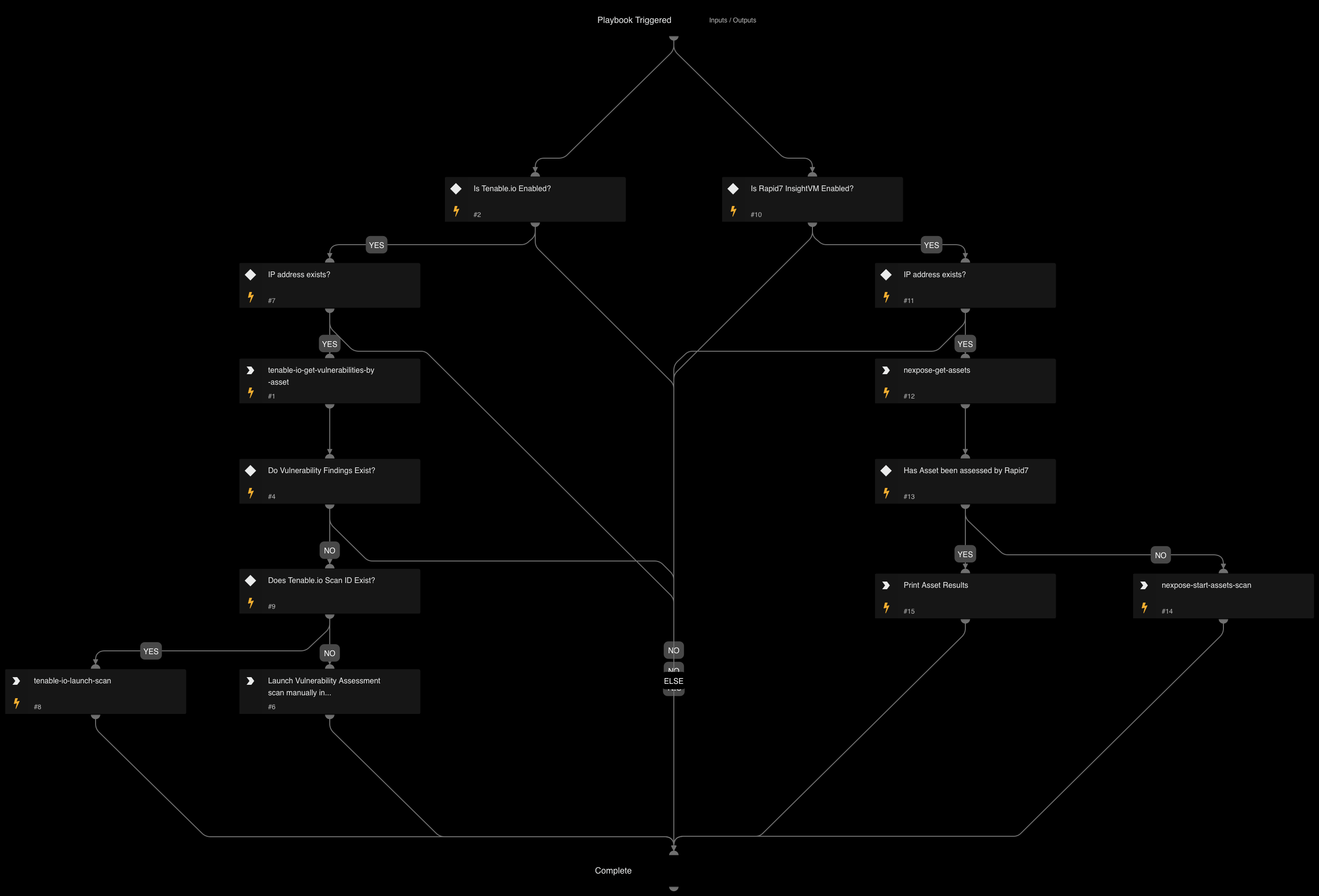
Playbook to Look up ASM discovered IPs in Tenable.io or Rapid7 InsightVM#
This playbook will look up an IP address in Tenable.io or Rapid7 InsightVM.
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
There are no sub-playbooks for this playbook.
Integrations#
- Tenable.io
- Rapid7 Nexpose
Scripts#
There are no scripts for this playbook.
Commands#
- tenable-io-get-vulnerabilities-by-asset
- tanable-io-launch-scan
- nexpose-search-assets
- nexpose-start-assets-scan
Playbook Inputs#
| Name | Description | Default Value | Required |
|---|---|---|---|
| IP | IP address to look up in VM tool. | True | |
| DaysPast | How many days to look in the past for scan results (Tenable only) | 30 | False |
| TenableScanId | Optional scan ID to provide for Tenable.io to use for scanning (Tenable only) | False |
Playbook Outputs#
There are no outputs for this playbook.
Playbook Image#