Cortex XDR - Cloud IAM User Access Investigation
This Playbook is part of the Cloud Incident Response Pack.#
Supported versions
Supported Cortex XSOAR versions: 6.8.0 and later.
Investigate and respond to Cortex XDR Cloud alerts where a Cloud IAM user`s access key is used suspiciously to access the cloud environment. The following alerts are supported for AWS, Azure, and GCP environments.
- Penetration testing tool attempt
- Penetration testing tool activity
- Suspicious API call from a Tor exit node
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
- Cloud Response - Generic
- Account Enrichment - Generic v2.1
- Cloud Credentials Rotation - Generic
- Cloud IAM Enrichment - Generic
Integrations#
This playbook does not use any integrations.
Scripts#
This playbook does not use any scripts.
Commands#
- ip
- xdr-get-cloud-original-alerts
- setIncident
Playbook Inputs#
| Name | Description | Default Value | Required |
|---|---|---|---|
| alert_id | The alert ID. | Optional | |
| autoAccessKeyRemediation | Whether to execute the user remediation flow automatically. | False | Optional |
| autoBlockIndicators | Whether to block the indicators automatically. | False | Optional |
| autoUserRemediation | Whether to execute the user remediation flow automatically. | False | Optional |
| credentialsRemediationType | The response playbook provides the following remediation actions using AWS, MSGraph Users, GCP and GSuite Admin: Reset: By entering "Reset" in the input, the playbook will execute password reset. Supports: AWS, MSGraph Users, GCP and GSuite Admin. Revoke: By entering "Revoke" in the input, the GCP will revoke the access key, GSuite Admin will revoke the access token and the MSGraph Users will revoke the session. Supports: GCP, GSuite Admin and MSGraph Users. Deactivate - By entering "Deactivate" in the input, the playbook will execute access key deactivation. Supports: AWS. ALL: By entering "ALL" in the input, the playbook will execute the all remediation actions provided for each CSP. | Optional | |
| AWS-accessKeyRemediationType | Choose the remediation type for the user's access key. AWS available types: Disable - for disabling the user's access key. Delete - for deleting the user's access key. | Disable | Optional |
| AWS-userRemediationType | Choose the remediation type for the user involved. AWS available types: Delete - for the user deletion. Revoke - for revoking the user's credentials. | Revoke | Optional |
| AWS-newRoleName | The name of the new role to create if the analyst decides to clone the service account. | Optional | |
| AWS-newInstanceProfileName | The name of the new instance profile to create if the analyst decides to clone the service account. | Optional | |
| AWS-roleNameToRestrict | If provided, the role will be attached with a deny policy without the compute instance analysis flow. | Optional | |
| shouldCloneSA | Whether to clone the compromised SA before putting a deny policy to it. True/False | Optional | |
| Azure-userRemediationType | Choose the remediation type for the user involved. Azure available types: Disable - for disabling the user. Delete - for deleting the user. | Disable | Optional |
| GCP-accessKeyRemediationType | Choose the remediation type for the user's access key. GCP available types: Disable - For disabling the user's access key. Delete - For deleting the user's access key. | Disable | Optional |
| GCP-userRemediationType | Choose the remediation type for the user involved. GCP available types: Delete - For deleting the user. Disable - For disabling the user. | Disable | Optional |
Playbook Outputs#
There are no outputs for this playbook.
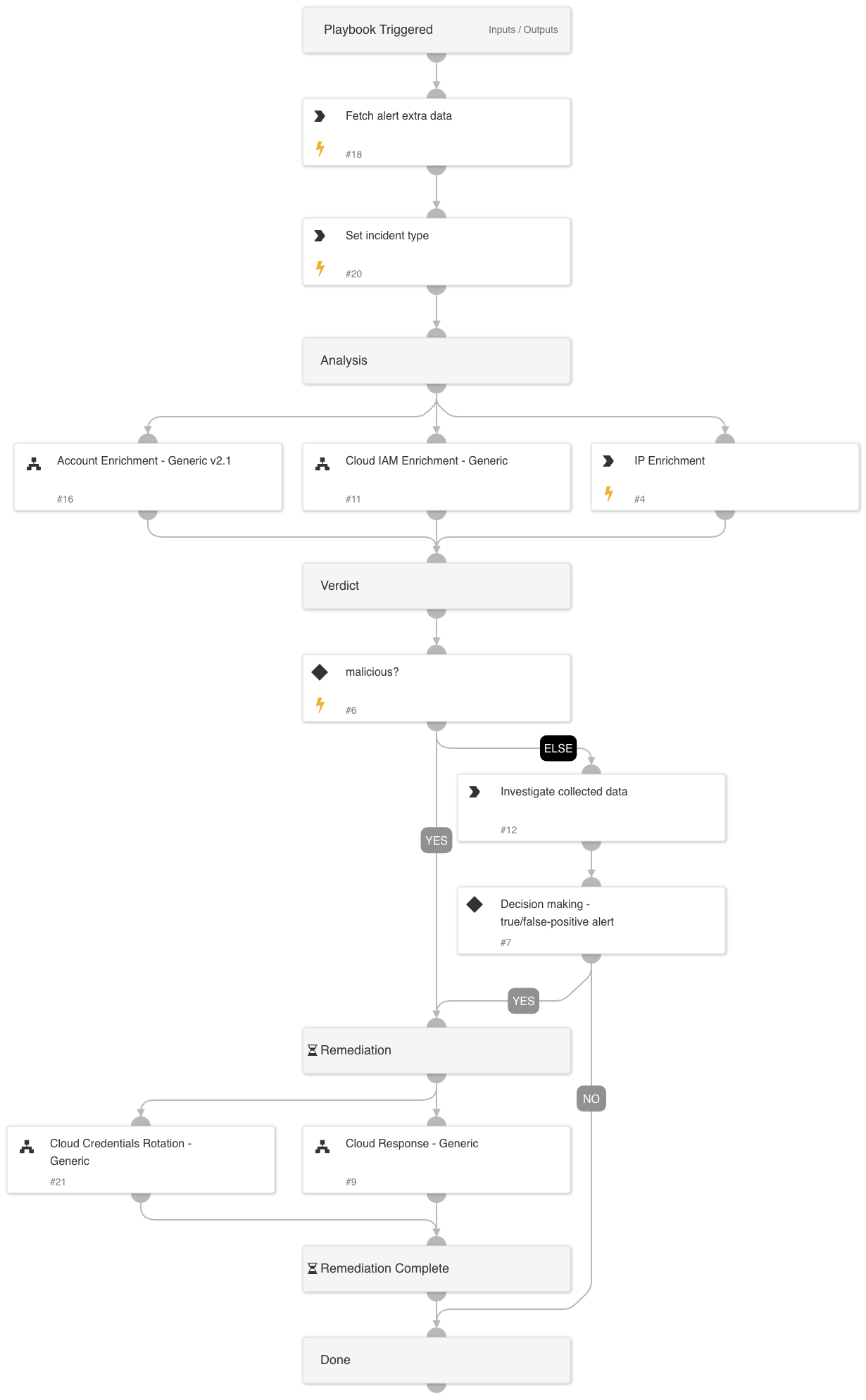
Playbook Image#