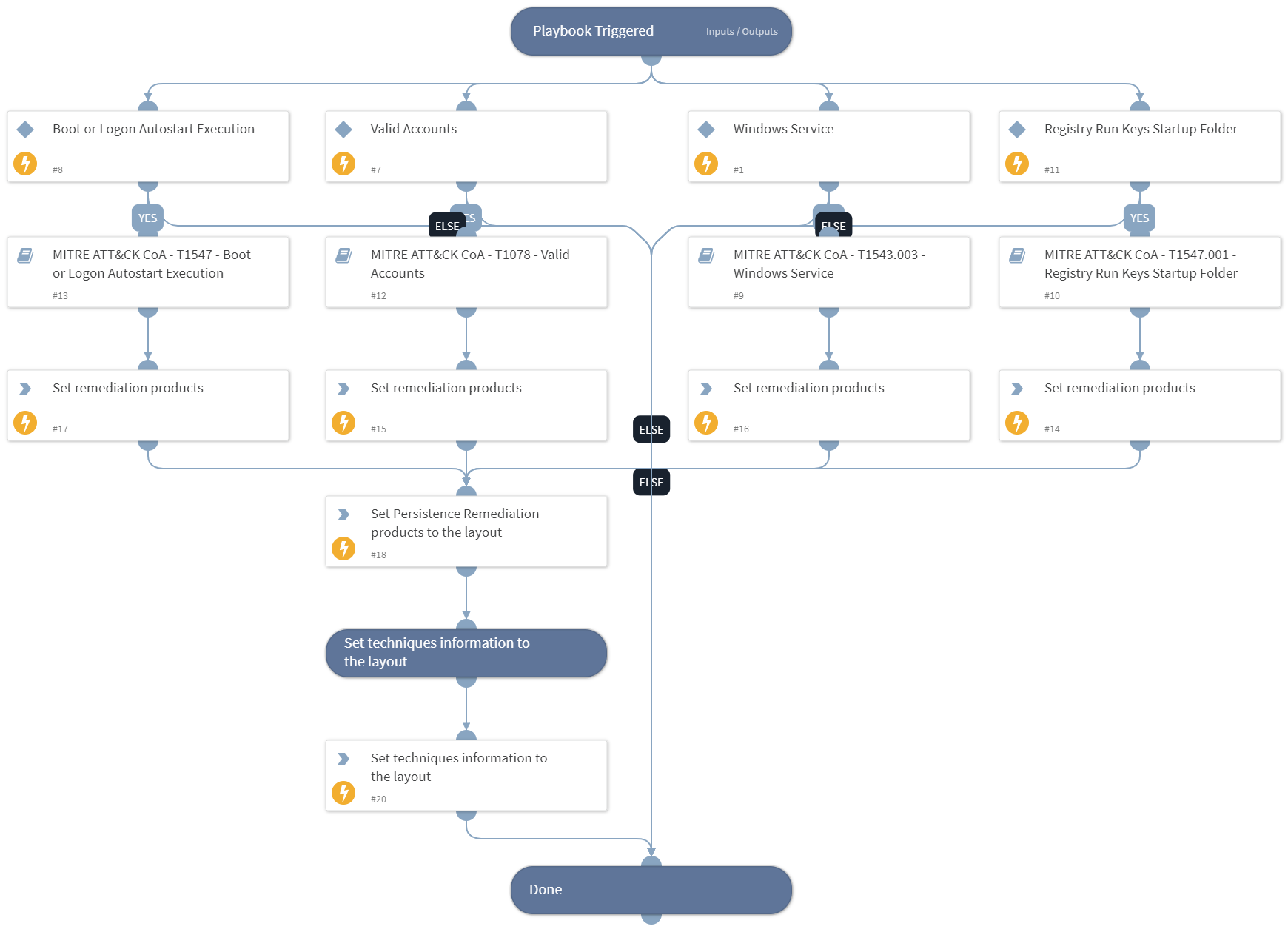
Courses of Action - Persistence
This Playbook is part of the MITRE ATT&CK - Courses of Action Pack.#
Supported versions
Supported Cortex XSOAR versions: 6.5.0 and later.
This playbook handles MITRE ATT&CK Techniques using intelligence-driven Courses of Action (COA) defined by Palo Alto Networks Unit 42 team. It utilizes each of the sub-playbooks for specific techniques that belong to this phase (tactic) according to the MITRE ATT&CK kill chain. The sub-playbook called depends on the technique input.
***Disclaimer: This playbook does not simulate an attack using the specified techniques, but follows the steps to remediation as defined by Palo Alto Networks Unit 42 team’s Actionable Threat Objects and Mitigations (ATOMs).
Tactic:
- TA0003: Persistence
MITRE ATT&CK Description: The adversary is trying to maintain their foothold.
Persistence consists of techniques that adversaries use to keep access to systems across restarts, changed credentials, and other interruptions that could cut off their access. Techniques used for persistence include any access, action, or configuration changes that let them maintain their foothold on systems, such as replacing or hijacking legitimate code or adding startup code.
Possible playbook triggers:
- The playbook can be used as a part of the “Courses of Action - Collection” playbook to remediate techniques based on kill chain phase.
- The playbook can be used as a part of the “MITRE ATT&CK - Courses of Action” playbook, that can be triggered by different sources and accepts the technique MITRE ATT&CK ID as an input.
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
- MITRE ATT&CK CoA - T1543.003 - Windows Service
- MITRE ATT&CK CoA - T1547 - Boot or Logon Autostart Execution
- MITRE ATT&CK CoA - T1547.001 - Registry Run Keys Startup Folder
- MITRE ATT&CK CoA - T1078 - Valid Accounts
Integrations#
This playbook does not use any integrations.
Scripts#
- SetAndHandleEmpty
- Set
Commands#
- setIncident
Playbook Inputs#
| Name | Description | Default Value | Required |
|---|---|---|---|
| technique | Mitre ATT&CK ID of a technique. | Optional | |
| pre_post | Rules location. Can be 'pre-rulebase' or 'post-rulebase'. Mandatory for Panorama instances. | Optional | |
| device-group | The device group for which to return addresses (Panorama instances). | Optional | |
| tag | Tag for which to filter the rules. | Optional |
Playbook Outputs#
| Path | Description | Type |
|---|---|---|
| Handled.Techniques | The techniques handled in this playbook | unknown |
| Persistence.ProductList | Products used for remediation. | unknown |
Playbook Image#