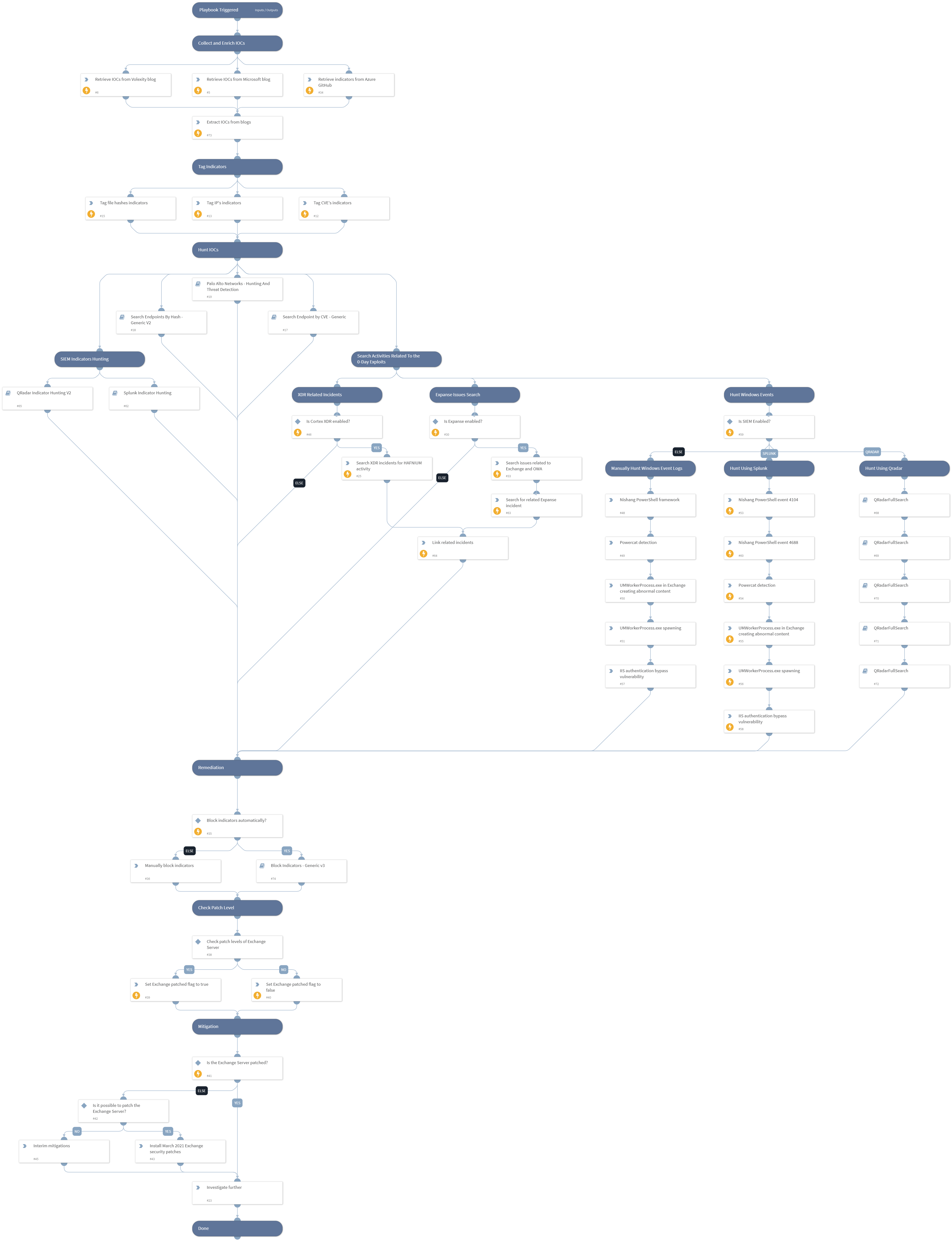
HAFNIUM - Exchange 0-day exploits
This Playbook is part of the Rapid Breach Response Pack.#
Supported versions
Supported Cortex XSOAR versions: 6.5.0 and later.
This playbook includes the following tasks: Collect indicators to be used in your threat hunting process Retrieve IOCs related to HAFNIUM and the exploited exchange 0-day vulnerabilities Discover IOCs related to the attack Query firewall logs to detect malicious network activity Search endpoint logs for malicious hashes to detect compromised hosts (Available from Cortex XSOAR 5.5.0). Block indicators Note: This is a beta playbook, which lets you implement and test pre-release software. Since the playbook is beta, it might contain bugs. Updates to the pack during the beta phase might include non-backward compatible features. We appreciate your feedback on the quality and usability of the pack to help us identify issues, fix them, and continually improve. Read more about the attack on our Unit42 blog: https://unit42.paloaltonetworks.com/microsoft-exchange-server-vulnerabilities/ Sources: https://www.splunk.com/en_us/blog/security/detecting-hafnium-exchange-server-zero-day-activity-in-splunk.html https://www.microsoft.com/security/blog/2021/03/02/hafnium-targeting-exchange-servers/
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
- Splunk Indicator Hunting
- Palo Alto Networks - Hunting And Threat Detection
- Block Indicators - Generic v3
- QRadar Indicator Hunting V2
- QRadarFullSearch
- Search Endpoint by CVE - Generic
- Search Endpoints By Hash - Generic V2
Integrations#
This playbook does not use any integrations.
Scripts#
- Set
- SearchIncidentsV2
- http
Commands#
- setIndicators
- linkIncidents
- splunk-search
- extractIndicators
- expanse-get-issues
Playbook Inputs#
| Name | Description | Default Value | Required |
|---|---|---|---|
| UserVerification | Possible values: True/False. Whether to provide user verification for blocking IPs. False - No prompt will be displayed to the user. True - The server will ask the user for blocking verification and will display the blocking list. | False | Optional |
| AutoBlockIndicators | |- Should the given indicators be automatically blocked, or should the user be given the option to choose? If set to True - no prompt will appear, and all provided indicators will be blocked automatically. If set to False - the user will be prompted to select which indicators to block. | True | Optional |
| InternalRange | A list of internal IP ranges to check IP addresses against. The comma-separated list should be provided in CIDR notation. For example, a list of ranges would be: "172.16.0.0/12,10.0.0.0/8,192.168.0.0/16" (without quotes). | lists.PrivateIPs | Optional |
Playbook Outputs#
There are no outputs for this playbook.
Playbook Image#