Hunt for bad IOCs
This Playbook is part of the Deprecated Content (Deprecated) Pack.#
Deprecated
DEPRECATED. Use the Search Endpoints By Hash playbook instead. Assumes that malicious IOCs are in the right place in the context and starts hunting using available tools.
Dependencies#
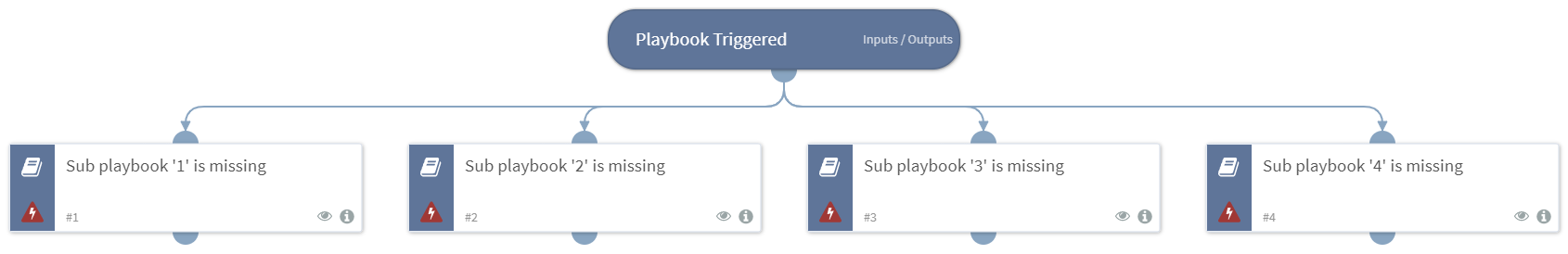
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
This playbook does not use any sub-playbooks.
Integrations#
This playbook does not use any integrations.
Scripts#
This playbook does not use any scripts.
Commands#
This playbook does not use any commands.
Playbook Inputs#
There are no inputs for this playbook.
Playbook Outputs#
There are no outputs for this playbook.
Playbook Image#