Suspicious Local Administrator Login
This Playbook is part of the Cortex Response And Remediation Pack.#
Supported versions
Supported Cortex XSOAR versions: 6.10.0 and later.
This playbook addresses the following alerts:
- Suspicious local administrator login
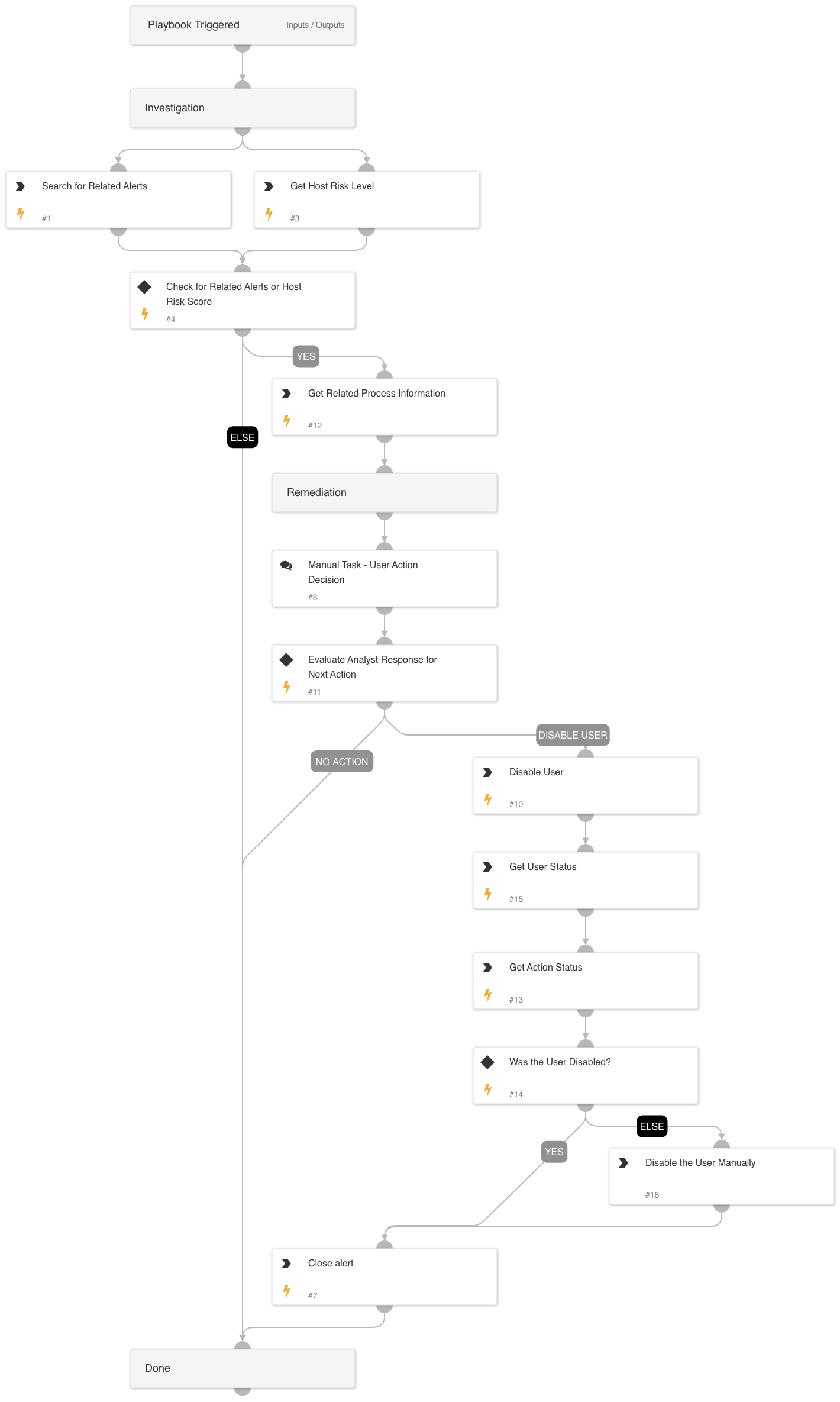
Playbook Stages:
Investigation:
- Retrieves the name of the process image involved in the alert.
- Checks for related Powershell/Command and Scripting/WMI alerts in the incident.
- Retrieves the host risk score.
Containment:
- Provide a manual task for an analyst to review the findings and decide the next steps.
- Possible actions:
- Disable User.
- Take no action.
Requirements:
- For response actions, the following integration is required: Core - IR.
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
This playbook does not use any sub-playbooks.
Integrations#
This playbook does not use any integrations.
Scripts#
- IncreaseAlertSeverity
- SearchAlertsV2
- get-endpoint-data
Commands#
- closeInvestigation
- core-execute-command
- core-get-cloud-original-alerts
Playbook Inputs#
There are no inputs for this playbook.
Playbook Outputs#
There are no outputs for this playbook.
Playbook Image#