User added to local administrator group using a PowerShell command
This Playbook is part of the Cortex Response And Remediation Pack.#
Supported versions
Supported Cortex XSOAR versions: 8.8.0 and later.
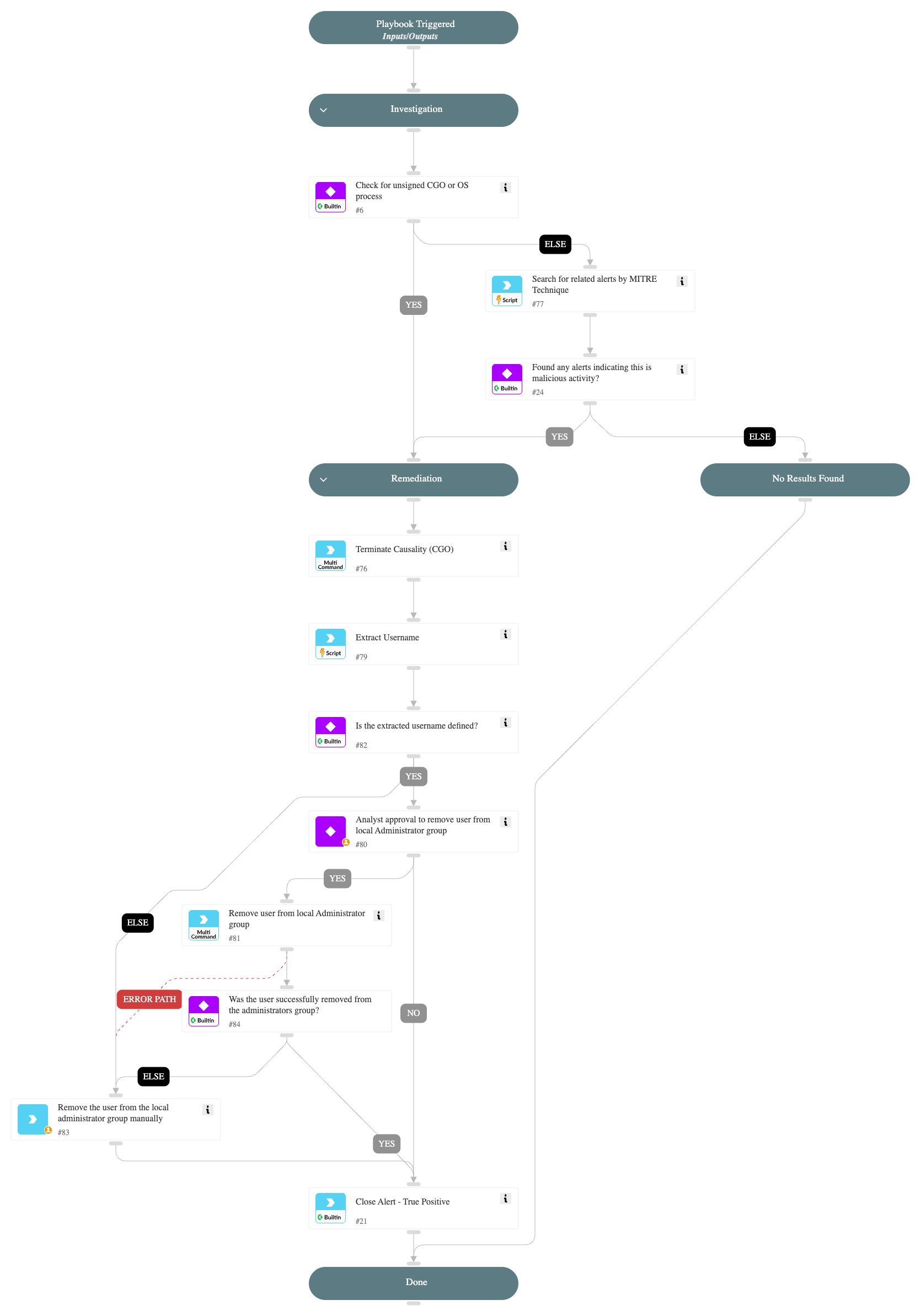
This playbook is designed to handle the alert 'User added to local administrator group using a PowerShell command'
The playbook executes the following stages:
Investigation: Check the following parameters to determine if remediation actions are needed:
- Cortex XSIAM alerts related to the hostname by MITRE tactics indicating malicious activity.
- Whether the process is unsigned.
Remediation: Handles malicious alerts by terminating the relevant processes and requesting the analyst's approval to remove the user from the local Administrators group. Handles non-malicious alerts identified during the investigation.
Dependencies#
This playbook uses the following sub-playbooks, integrations, and scripts.
Sub-playbooks#
This playbook does not use any sub-playbooks.
Integrations#
This playbook does not use any integrations.
Scripts#
- SearchIncidentsV2
- Set
Commands#
- closeInvestigation
- core-execute-command
- core-terminate-causality
Playbook Inputs#
There are no inputs for this playbook.
Playbook Outputs#
There are no outputs for this playbook.
Playbook Image#